How Using the SLAM Method Can Improve Phishing Detection
Phishing is usually the number one topic to cover when it comes to cyber security training for your staff… and for a good reason.
Over the past few decades, phishing has been the primary method for cyber attacks on businesses and individuals in Melbourne and the wider world. For example, phishing emails often launch ransomware attacks, credential theft, and database breaches.
Phishing has remained an ever-present threat simply because it is effective – scammers continually catch victims out with this kind of approach. They also regularly evolve their methods as technology continues to develop. For example, scammers use AI-based tactics to make phishing more efficient and, therefore, more dangerous.
Scammers would move on to another method if phishing wasn’t so effective… but victims continue to be tricked. They continue to open malicious attachments, click on dangerous links on emails and texts, and divulge personal information.
Some damning figures show the prevalence and growth of phishing; for example, in May 2021, phishing attacks increased by 281%! In June of the same year, they grew by another 284%.
Good businesses will provide regular cyber security training for their employees. However, studies have shown that employees are much more likely to fall victim to a phishing scam as soon as six months after training. This is because they forget what they learned at their last training session!
Provide a ‘hook’ that your staff can use for memory retention to remain vigilant against phishing scams. The SLAM method of phishing identification is perfect for this.
What is the SLAM Method to ID Phishing?
People have been using acronyms to help retain information for a long time, and this technique can work for your cyber security training and phishing identification. The SLAM acronym covers four critical areas of an email message, which must be checked before you can fully trust the email and its contents.
SLAM stands for:
- S – Sender
- L – Links
- A – Attachments
- M – Message text
When your employees utilise the SLAM technique, it takes far less time to check the suspicious email and either delete it or confirm that it is authentic. All they need to do is use the cues provided in the acronym.
And as Melbournians, your staff will probably enjoy using acronyms! We have plenty… MCG, NGV, ACMI, AFP… the list goes on!
Check the Sender
The first step in the SLAM technique is to take a close look at the sender. Unfortunately, scammers will either spoof an email address or look alike, which may appear to be the real thing without close inspection. Unfortunately, people do fall victim to this regularly.
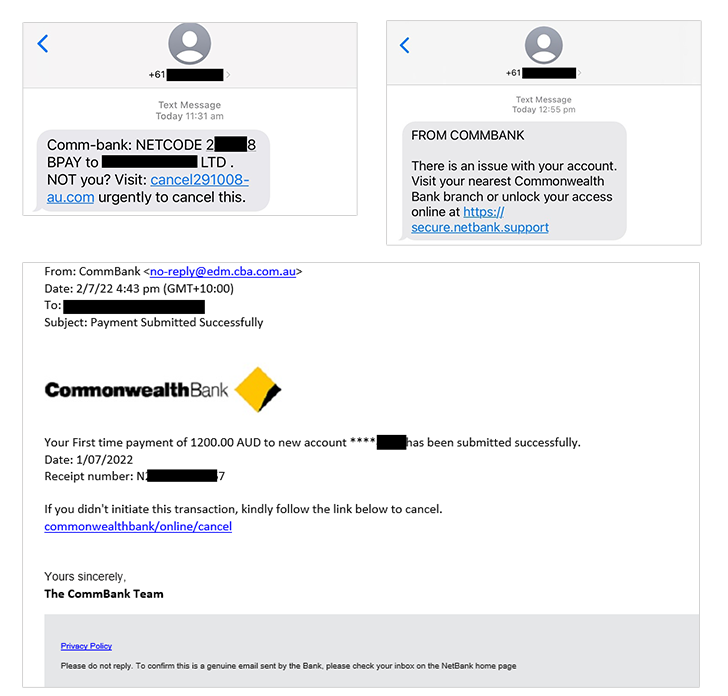
Take a look at this example below. The email address domain is “@cba.com.au” The scammer is trying to impersonate the Commonwealth Bank of Australia. They do this to try and trick the reader into clicking on the link or opening the attachment because the domain that they have created looks as though it could be genuine.
The email itself is persuasive and has probably fooled over a few people into divulging their details. In this case, that would include their login number and password for their online banking account.
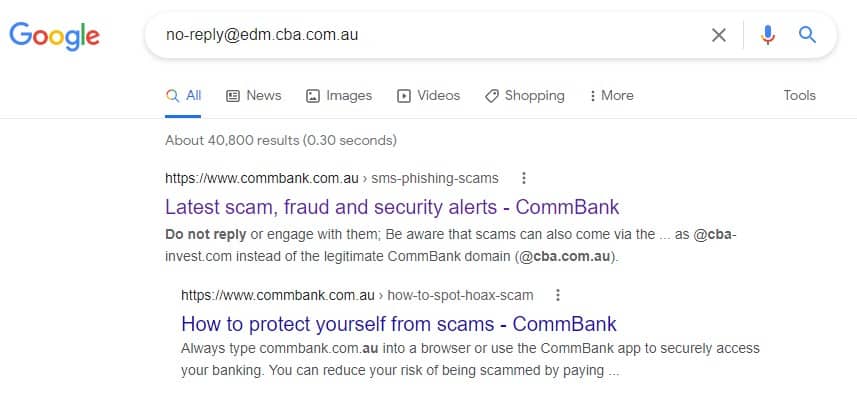
Noting the email address and pasting it into Google will show that this is a phishing scam. And it’s not just an email scam but has also appeared in text message form.
It only takes a moment to search for an email address. This moment is critical in defending your business and sensitive information from phishing scams.
Hover Over Links Without Clicking
Hyperlinks are popular in emails, and unfortunately, they can often bypass antivirus and anti-malware filters. These filters identify file attachments containing malware… but a link to a malicious site won’t have any destructive code… however, the website it takes the victim to does.
Links can appear in an email in several ways, including hyperlinked words, images and buttons. If you’re viewing an email on a computer, it’s important to hover over links before clicking on them so that you can view the actual URL. Doing this is an excellent way to catch dodgy links.
This is more difficult to do on a mobile device, so we recommend that you don’t click on the URL. Instead, go to the purported website to check the message’s validity. In the case of the previous email, that would be the official Commonwealth Bank site.
Never Open Unexpected or Strange File Attachments
File attachments are a vital part of scammers’ strategy when using phishing emails. For example, some emails carry an attachment that appears to be a Word document for something such as a ‘large sale order’. Often, the victim clicks on this attachment out of interest.
It’s getting tougher to identify suspicious attachments and understand which file formats you should not open. These cybercriminals are becoming more cunning and are infecting more and more types of documents with malware… even PDFs! One example of this is fake event tickets, so if you’re waiting for tickets to a gig at Rod Laver, beware of dodgy PDF documents in your inbox.
A good policy is never to open strange or unexpected file attachments. Moreover, make sure you use an antivirus or anti-malware application to scan incoming emails and their attachments.
Read the Message Carefully
Always read the email content carefully.
As a society, we’ve become very good at scanning through the text quickly as we consume more content daily. This ability to read quickly helps us process plenty of information, but it also means you might miss something important. And if you don’t read a phishing email carefully, you will miss the telltale signs.
Many phishing emails contain grammatical and spelling errors, so if you spot these, be wary.
Get Help Combating Phishing Attacks in Melbourne
The proper training and software can help eliminate phishing attacks in your Melbourne business. For expert advice and protection, get in touch with us today.

About the author
Yener is the founder and Managing Director of Intuitive IT. Prior to running his own business Yener worked for a number of corporate organisations where he gained invaluable experience and skills, as well as an understanding of how IT can complement and improve business outcomes.